New on LowEndTalk? Please Register and read our Community Rules.
All new Registrations are manually reviewed and approved, so a short delay after registration may occur before your account becomes active.
All new Registrations are manually reviewed and approved, so a short delay after registration may occur before your account becomes active.


























Comments
Well it's true they died in 2013/2014, if not in 2009 when they got hacked firstly and then upgraded to vb4 when everyone wanted them to stay on vb3
Collision Resistance != Decryption.
There's a 2^18 collision attack against MD5. There's a 2^123.8 decryption attack against MD5. Having something generate the same hash only allows you to authenticate to the same website.
Because SHA-256 has no known attack against the full algorithm, only reduced-rounds variants thereof (at least, per a quick wikipedia lookup).
This is just another lesson for people not to use the same passwords on multiple websites and stop using insecure passwords. Regardless how the password is stored in a database (as long as it's not plain text), the strength of your password is critical to your own security.
MD5 is also one way, and can not be decrypted. What you can do is encrypt all the possible passwords in the world, store the result in a database, and then search for the MD5 hash - it's not easy, though.
Also impossible with salt.
http://www.webhostingtalk.com/showthread.php?t=1584028
@splitice looking for a WHT ban?
I'm still betting that they cover it all up in a few days and delete that topic
They can try it's on archive.org
it's on archive.org
Not if the attacker knows the salt method.
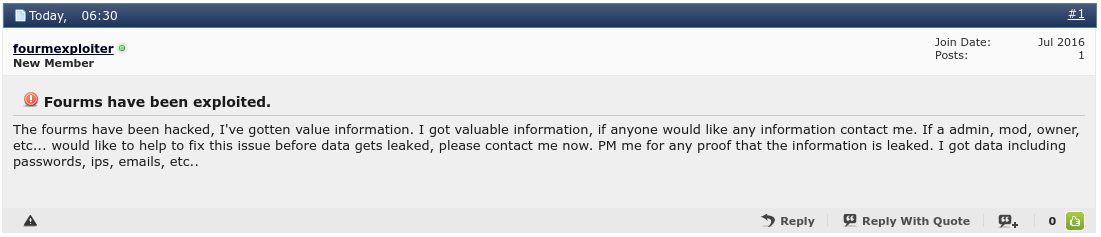
This just got posted on WHT:
Not only does that look fake but it looks dumb considering the DB is already out there.
Not fake? See 4th post: (edit - post deleted at Wht)
LOL! @Licensecart is really upset with my posts and his inability to read.
No kidding
It's still fun seeing people trying.
Jeez
Thanks for the heads up.
You can't decrypt hashes because it's never encrypted. If you want to crack a hash you could just post your list on the Hashkiller.co.uk forum, you don't even need GPU's and a huge wordlist.
Salting in vbulletin is pretty much useless.
Hey, at least I know my data is secured by dragon
-happy SD customer
Well, what did you expect... ;-)
Always the most ridiculous part of WHT to me, and a clear sign they're more interested in advertising dollars than actual participation.
Make zero difference if the user chooses "password" as their password, though.
Ow and expect my business with you to be gone next month. Bye bye $30/month
Im pretty sure the only thing they do when importing is save then vb auth and wait for the imported users to login. When signing in they check the info with vbs auth functions and if it's right save the password using blestas function.
Vbulletin is pretty horrible though.
Well I can't find anyone with Domin43 or Domain43, so if you are a real customer you claim to be feel free to DM me your client ID or post it here since it's a 4 digit number, and I'll schedule a cancellation at the end of the month for you no skin off my nose...
no skin off my nose...
We should be concentrating on wht than diverting ..
@Licensecart is an ass. He reported me to fraudrecord for not paying an invoice, probably a Blesta license. So anyone who orders something from him and stops renewing it, will be reported in fraudrecord. This guy is hilarious and annoys the fuck out of me always talking about Blesta.
Well, his unprofessionalism has no bounds, it could be seen in multiple occasions already. Lol, I would happily buy direct rather from unethical resellers, regardless of the benefits it can ever bring.
Did you get your record off FraudRecord, though?
Have they still not made any form of public announcement about it..?
For sure!
No, I haven't, I think he's the only one who can remove it IIRC?
Ah that sucks. Well I'll just say this. @LicenseCart go fuck yourself.