All new Registrations are manually reviewed and approved, so a short delay after registration may occur before your account becomes active.
German Police Raid DDoS-Friendly Host ‘FlyHosting’
 treesmokah
Member
treesmokah
Member
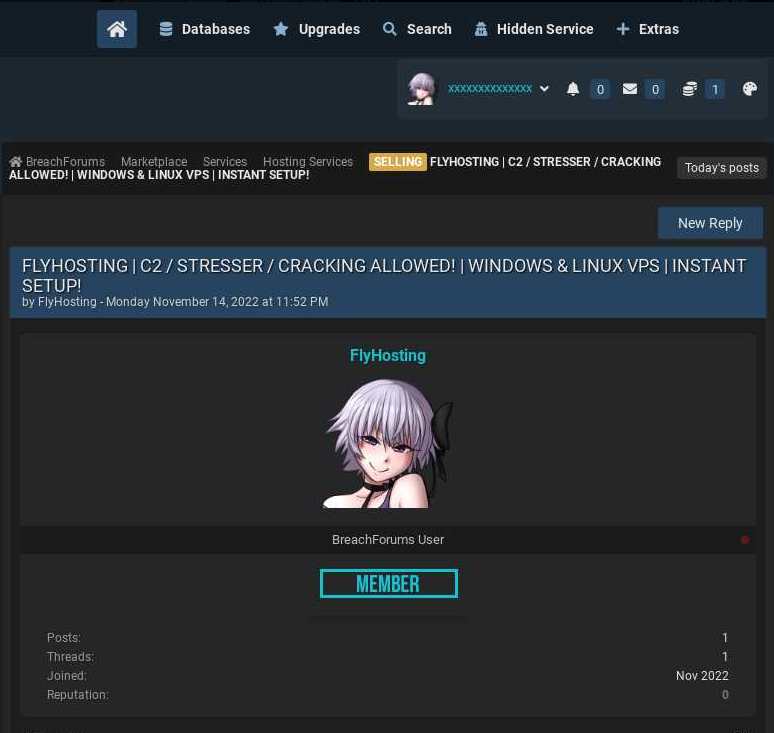
A statement released today by the German Federal Criminal Police Office says they served eight search warrants on March 30, and identified five individuals aged 16-24 suspected of operating “an internet service” since mid-2021. The German authorities did not name the suspects or the Internet service in question.
“Previously unknown perpetrators used the Internet service provided by the suspects in particular for so-called ‘DDoS attacks’, i.e. the simultaneous sending of a large number of data packets via the Internet for the purpose of disrupting other data processing systems,” the statement reads.
News of a raid on FlyHosting first surfaced Thursday in a Telegram chat channel that is frequented by people interested or involved in the DDoS-for-hire industry, where a user by the name Dstatcc broke the news to FlyHosting customers:
“So Flyhosting made a ‘migration’ with it[s] systems to new rooms of the police
,” the warning read. “Police says: They support ddos attacks, C&C/C2 and stresser a bit too much. We expect the police will take a deeper look into the files, payment logs and IP’s. If you had a server from them and they could find ‘bad things’ connected with you (payed with private paypal) you may ask a lawyer.”
https://krebsonsecurity.com/2023/03/german-police-raid-ddos-friendly-host-flyhosting/
edit;
https://web.archive.org/web/20230210085733/https://flyhosting.de/en/
someone did shitty archiving job so we only have the frontpage, no impressum which could point on who was running the shitshow.
to anyone archiving hosting providers etc, get an account on archive.org which is free and then you can archive full page + all sublinks(for extra sanity, you can also manually archive on archive.today)
















Comments
ASN: AS202437 (company info)
Previous upstream: AS49581 (Tube-Hosting)
(safe to say SkyLink data center was raided, @HostSlick / @combahton_it do you know anything about that?)
Used sub: 185.132.53.0/24 (abuseipdb)
edit;
another company and network ran by the same person;
https://suite.endole.co.uk/insight/company/14658444-anoneox-ltd
https://bgp.tools/as/199847
I've bought a VPS from them before. Never really used it.
When I bought it, they were using AS200303 - 45.95.55.0/24
It still shows up as flyhosting https://bgp.he.net/net/45.95.55.0/24#_dns
Thanks for letting us know.
This IP looks like BYOIP on https://lumaserv.com/.
IF they used their German loc(and that's very likely, their NL loc was SkyLink) then Combahton German DC got raided as well. Looks like they are either in the same DC, or they got Transit/DDoS-Protection from Combahton.
How can you be smart enough to set up an Ltd (not that it require major IQ but still)
Yet dumb enough to under your legally registered company advertise "STRESSER CRACKING ALLOWED"?
I just don't get it
Yeah, they should’ve learn how to hide it from northlayer.
Iceland servers for booters would be absolutely aids.
Bandwidth there is extremely expensive, and large booters need several 100Gbps links minimum - not to mention IPHM.
WAY too much of daddys money has been spent: https://bgp.tools/as/59788
I think he just meant that they should have learnt from KUBBUR/NorthLayer how to not be transparent
Isn't this host ran by serial exit scammer or some shit?
I remember a drama and his name turns lights in my head.
Let's just say it wasn't very well planned out :P
"Raided" just Sounds too extreme lol
Usually you build up Co-Operation with the authorities in all years. German BKA for example has a hosting provider contact database and you have a permanent contact person with them.
When they want seize some server you arrange a date and time with them to appear.
Then usually two guys arrive in a car with a court order and you Escort them to the Rack where they can pull SSDs/HDDs or copy them and leave again.
There must be very strong proof that they (flyhosting) loose their immunity and the authorities are doing this. I. E. there is proof that they are Involved in this illegal activities
Interesting theory, however we never had a 'raid' by authorities in our DC or Points of Presence
Speaking as of today, AS30823 transits about 500 ipv4-prefixes, there are multiple downstreams in our network, which either just have an uplink or tunnel with us, so they just utilize our DDoS-Protection and Transit, however they do not colocate / rent any hardware with us. If you have any case related questions, you better ask our customers.
Speaking of sending in the egress large scale DDoS-Abuse, it would be just a matter of time once we get to know about it - thats the last time then, you're using our network.
They offer IPHM for colo customers, bandwidth costs are probly indeed aids.
Thanks to both of you, @combahton_it and @HostSlick.
I was just "thinking loud", I of course did not want to accuse anyone without evidence.
Ironically, Flyhosting themselves was reporting IP's on AbuseIPDB
https://www.abuseipdb.com/user/105015
I hope now the police taught them a lesson for all the things they have done. And i hope every kind of this provider type should be jail asap. Great Job Germany Police
why even lol
I don't think this single raid caused so much damage as described by you, but as I can see, LEA are actively working on the illegal DDoS-for-hire market. That's really good.
Owner will receive slap on the wrist and will continue his operations from another jurisdiction.
Isn't he was arrested?
Is that why you scattered and deleted x33.biz... but left it under the same CloudFlare account as HS? lol
https://web.archive.org/web/20220331024203/https://x33.biz/
https://find-and-update.company-information.service.gov.uk/company/14463241/officers
https://find-and-update.company-information.service.gov.uk/company/08786264/officers
@twc hmm also
https://www.ipvolume.net/ (i swear to god i saw another copy of this crap named same ip volume but cant remember the site url, something like anonymous vpn or so)
https://colocationx.com/ (like wtf?)
https://www.abuseipdb.com/check-block/193.142.146.0/24
https://viz.greynoise.io/query/?gnql=metadata.asn:AS208046
Edit: best part on colocationx website - check the title - ClocationX Ltd. - Secure and Reliable DataCenters in Amsterdam
Second edit: found it https://web.archive.org/web/20210507100156/http://ipvolume.org/
Means absolutely nothing.
Do the same with OVH or Hetz, you will be surprised.
@treesmokah someone spoofing ip sources or what? no way hetzner or ovh would have that many servers scanning them? or am i wrong?
Spoofing is extremely hard, if not impossible nowadays - your traffic will be dropped by Tier 1's. In HS case, its a false flag.
Regarding scanning, yes - they do, from big providers especially DigitalOcean.
Scanning is relatively harmless, not illegal and you wont get on Spamhaus kill list for it.
According to crowdsec: https://www.crowdsec.net/blog/crowdsec-community-report
1. Deutsche Telekom
2. Chinanet
3. AMAZON
4. DigitalOcean
5. Vodafone
6. China Unicom
Scanning without consent of provider is forbidden in most normal hosting services. It's like trying to see if doors are closed/open by wobbling door handle. Very if'y and highly not recommended.
In case anyone want to test my blaber, you are free to do that. Furthermore, here is a nice tool for that: https://github.com/robertdavidgraham/masscan
Knocking ports is not bad, and can be used as intelligence strategy.
What do you think Censys, Shodan etc do? The exact same thing, and oy vey - without permission!!!
I’d say the vast majority of people buying a $2 VPS to port scan are not in the bussiness of conducting an advanced intelligence strategy.
You don't know that