New on LowEndTalk? Please Register and read our Community Rules.
All new Registrations are manually reviewed and approved, so a short delay after registration may occur before your account becomes active.
All new Registrations are manually reviewed and approved, so a short delay after registration may occur before your account becomes active.
HAZI.ro | Dedicated vCPUs | Up to 16 addon IPs | No SMTP | 40% OFF Recurring
 FlorinMarian
Member, Host Rep
FlorinMarian
Member, Host Rep
in Offers
Hello, dear community!
Since last time the sales went very well, we renewed this offer in order to reach, we hope to completely exhaust this server this month as well, and we will buy a new one.
We offer a 40% recurring discount for all virtual dedicated servers if you use the discount code JUNE-DEAL
VDS - 2vCPU - 4GB RAM - 120GB SSD Enterprise
- 2x Dedicated vCPUs 2.30GHz ↗ 3.60GHz
- 4GB RAM DDR4 ECC 2133MHz
- 120GB SSD Enterprise RAID10
- 1Gbps Connection (Shared)
- Unlimited Monthly Traffic (10TB @1Gbps then Unlimited @100MBps)
- Voxility 1Tbps AntiDDoS Protection
- Price: 4.20 EUR/mo
- Purchase it here
VDS - 4vCPU - 8GB RAM - 240GB SSD Enterprise
- 4x Dedicated vCPUs 2.30GHz ↗ 3.60GHz
- 8GB RAM DDR4 ECC 2133MHz
- 240GB SSD Enterprise RAID10
- 1Gbps Connection (Shared)
- Unlimited Monthly Traffic (10TB @1Gbps then Unlimited @100MBps)
- Voxility 1Tbps AntiDDoS Protection
- Price: 9.00 EUR/mo
- Purchase it here
Physical server:
- CPU: 2x E5-2699 V3 36 Cores / 72 Threads (2.30GHz ↗ 3.60GHz)
- Memory: 12x 16GB RAM DDR4 ECC 2133MHz
- Storage SSD: 6x Samsung PM893 Enterprise 1.92TB
- Network: 4x 1Gbps
- Protection: Voxility 1Tbps AntiDDoS
Service features:
- Dedicated Physical Thread per vCPU
- KVM Virtualization
- NoVNC Console Access
- Integrated Control Panel
- 1-click Operating System Installation
- Intrusion Prevention System
- Intrusion Detection System
Operating Systems:
- CentOS 7 64bits
- CentOS 8 64bits
- CentOS 9 64bits
- Debian 9 64bits
- Debian 10 64bits
- Debian 11 64bits
- Ubuntu 18.04 64bits
- Ubuntu 20.04 64bits
- Ubuntu 22.04 64bits
- FreeBSD 12.x 32bits
- FreeBSD 12.x 64bits
- FreeBSD 13.x 32bits
- FreeBSD 13.x 64bits
Useful information:
Looking Glass: Click here
Terms & Conditions: Click here
Accetable Usage Policy: Click here
Privacy Policy: Click here
Accepted payment methods:
- MobilPay (Visa / Maestro / Mastercard)
- Paysafecard
- Bitcoin
- Ethereum
- USD Coin
- Dogecoin
- Litecoin
- Dai
- Bitcoin Cash
- Bank Transfer
















Comments
A single YABS triggers "permanent mitigation" that your network speed would decrease to less than 20 Mbps.
A single "abuse", including zero day attack that is not your fault, causes service deletion with 30-minute notice and no second chances.
You're fully right. My server was canceled without previous warnings or any without any contact attempts
True Story. However, I would like to know how you know when the client is being abused or the server has been compromised as long as you DO NOT HAVE ACCESS TO ITS VM.
I'm sure you also received a record of what happened to your deleted VM. If it's your fault, take it, if not, secure your VM next time.
So what's in the record?
Is there a forensic image of the disk and a capture of the network traffic?
If it's just a report or complaint letter, it's insufficient for the customer to reproduce the problem, and it's insufficient to prove that the "abuse" is an intentional act of the customer.
However, I would like you to answer my question. How do you if the client abused or his VM was compromised when your client came to you a few days ago, he has false identification data and obviously you do not have access to his KVM.
sounds like its guilty until-
Hi @FlorinMarian!
Hope your sales are going great!
If a customer signs up with fully satisfactory identification, would that change your mitigation procedures?
May I please ask what is a "vcpu" for you and how you determine when the server capacity is "exhausted?"
Thanks!
Friendly greetings from Mexico!
Tom
If the abuse does not occur immediately after purchasing the service and the service is prepaid for a longer period, certainly.
I was referring to the assignment of all 72 physical threads of the server.
As for RAM / Storage, we still have free slots for doubling the RAM memory (without replacing some DIMMs with others of higher capacity) and we also have empty caddies for 2 SSDs.
Best regards, Florin.
I guess you mean that when 72 vcores are assigned to VMs, then the server is exhausted? So, if only plans with 2 vcpus per plan were sold, the server would be exhausted when 36 plans were sold?
Thanks!
In the case of dedicated virtual servers, yes.
Instead, in the case of KVM Romania servers that have the same processor but with a slightly smaller number of threads, we offer only 50% dedicated CPU, so 128 packages can be sold there.
Plain and simple scam. Such "provider" should be banned and go to hostloc for the clients. A true shame. I run YABS on cron 24/7 and if any provider "ban" me for such actions I would simply sue him. Disgusting.
You won't get banned by running YABS.
The IP address is throttled by "mitigation" until you open ticket and promise not to YABS again.
You avoid the real question and become just one of the crowd, it's a shame for you.
Regarding YABS, I received that answer from Datacenter, I pass that on, there is nothing to discuss on this side.
You know the story of UDP + permanent mitigation since you were my client, now that the ping and UDP don't fall into permanent mitigation, you are exaggerating the remaining issue.
This is not what's important here. From what I understand, there's two types of people here.
For the first group of people, it's really up to you as a business owner how you want to handle abuse reports. While I don't need romanian servers, I belong to the second group and think it's ridiculous how you provided a 30 min notice for the one person who you believed got compromised.
At the very least, provide access to files because you know as well as I do that not everyone does backups. It poses zero risk for you to provide nothing but access to your clients' files.
I don't want to be mean but I don't think you did your math on this server.
If 36 vps means full server @ 4.2 euro/month you make 150 euro/m. If we subtract the colocation fee (~70 euro/m) and the IPs at 0.5 euro (18 euro) you remain with 62 euro. Your samsung Hard-disks cost was 2400euro.
At this calculation with 62euro/m revenue per server you need 3 years just to get your Hard-disk money back. I did not included you salary for the support, the rest of the server, taxes, fees and maybe licenses.
In his situation you need to oversell hard the cpus to make a profit.
Wish you best luck with this endeavor.
I believe they did their math and there are some things about the hosting market on LET that should be left unsaid. Your calculations are off and not the right way to calculate these things because not only did they sell some of these plans for 3.50, they also have to pay payment processing fees. Also, consider that maybe some of their customers are paying normal price (or way above normal price for b2b customers)
Assuming they don't thin provision disks, you get a different picture if you work out the math. If they do thin provision disks... I'm not saying they do this or that but let's not bash their sales thread and assume similar things happen for most providers. That's the way the math checks out on LET especially for the "cheap" deals.
Thanks for the tips!
Yes, I said and I repeat, it was not an inspired decision.
In the future, when there are more such cases, I will use a method that I thought of now, namely to block any Outbound access from the Firewall except SFTP but this only in the case of customers I trust (old customers, real identification data, more services purchased and so on)> @AndreiGhesi said:
Thanks for the calculations but omit a few things:
1. IP addresses cost 1200 euros the first year then 480 euros for each subnet /24 anually
2. The SSDs from Samsung were sold for only 850 RON each, but being part of a Bulk, they have only a 6-month warranty (purchase made from the company whose object of activity is to repair laptops, not OLX or another person unauthorized and unfortunately they didn't have 10 pieces as much as I would have liked to buy, somehow the 6 pieces in their stock got lost)
Website down due of botnet attack layer7.
I'll take my lunch then I'll take care of it.
Thanks to the person who did this, I really needed help in supporting my arguments that not everyone deserves to be treated as a victim, not as an aggressor.
Website UP & Running (even if attack is still active).
You shouldn't have delivered the service if the identification data is false.
Someone has a strong toy that keeps our site down.
We have blocked in the last 30 minutes no less than 3,667,878 IP addresses, a clear sign that ours is abusing a provider that does not have ip spoofing under control.
Cloudflare Enterprise Plan blocks all strong toys.
Come on people... whoever is doing it, don't be an asshole.
Feel free to criticize host if you feel that's justified. Damaged reputation is painful enough, just don't cause him additional damage with the ddos and crap. It's not like those small business sole proprietorships are rich or something. Don't mess with people's livelihood.
It’s all about config I think
would recommend giving Cloudflare a try. Sucuri WAF is another option starting at $10 but gives a lot of false positives in my experience
I know it can be stressful when your site is the victim of such an attack
It's been over 33 hours since our site was unavailable, dealing with a 24/7 attack.
I tested:
Unfortunately, of those tens of thousands of IP addresses that are part of the attack, some go beyond any possible filter.
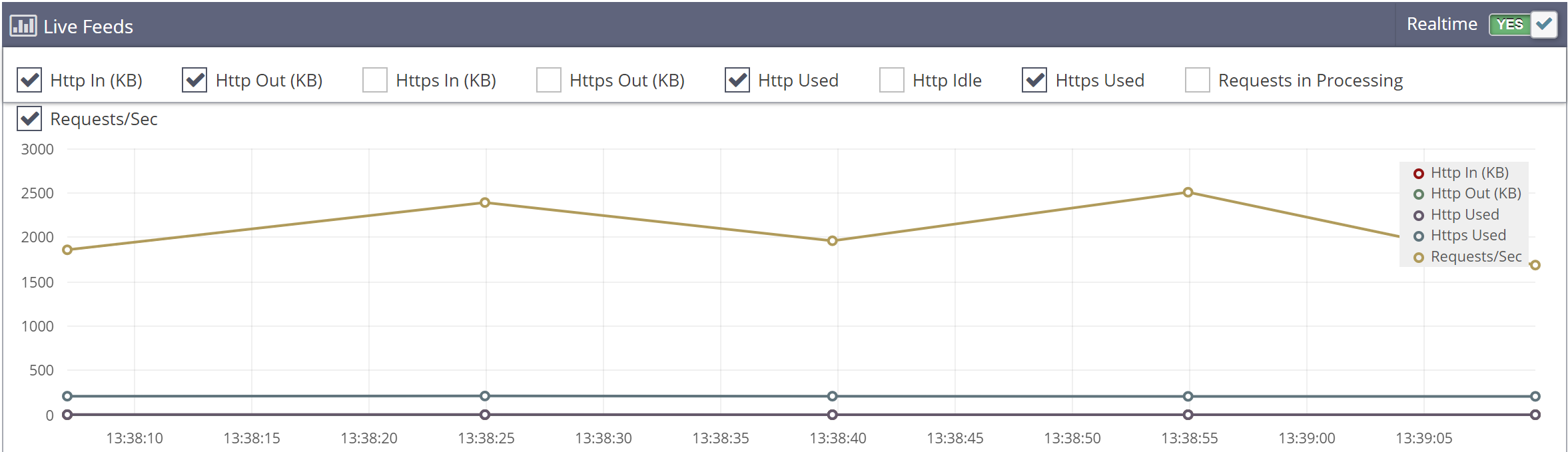
To understand how big the impact is, I have attached two screenshots from both the free and the purchased protection offered by CloudFlare. Both are junctions, our site being hit with 800-8000 simultaneous connections.
We will try again tonight to resolve the situation on our own and if we do not succeed, we will address the competent bodies that can investigate cybercrime.
Cloudflare would help but it's probably much less effective when your origin IP is known to your attackers and no firewall on your http/https ports. Are they only attacking you through cloudflare?
It would be nice if the authorities would catch the ddos kiddies for you but unfortunately I don't think that will happen. Previously, there were people attacking various LET hosts and demanding crypto ransoms and there's quite a lot of people around here who could probably help you out.
The data was collected in about 24 hours, the rest of the time I used only the protections offered by iptables / litespeed / recaptcha.
Except... he does have a load of IPs because he sells VPSes. He could temporarily copy his website onto one of them and have cloudflare use that, or have a wireguard tunnel from a VPS to his original machine and close off the standard ports on that, or even just get another VPS from someone else and use that for now so he's got an IP in someone else's range.